Don't just believe the 'Safe and Secure' label. Learn the simple browser trick that reveals if a website is secretly stealing your data.
Every website claims to be "Private." They all have a green lock icon. They all have a "Secure" badge. But how do you know? In the physical world, you can check if a door is locked. In the digital world, you often feel blind. But you have a superpower you might not know about. It's built into your browser, it's free, and it never lies. It's called the **Network Tab**.
At MojoDocs, we don't just want you to trust us; we want you to verify us. In this guide, we will teach you the simple skill that advertisers and data brokers hope you never learn: How to see the invisible data leaving your computer.
Step 1: Open the "X-Ray Vision"
You don't need to be a hacker to do this. Open any website (try it on a cloud converter).
1. Right-click anywhere on the page and select Inspect (or Inspect Element).
2. A panel will open. Click on the tab labeled Network.
3. This is your radar. It shows every single piece of data entering or leaving your browser.
Step 2: The "Upload Test"
Now, try to convert a file on that site. Keep your eyes on the Network tab.
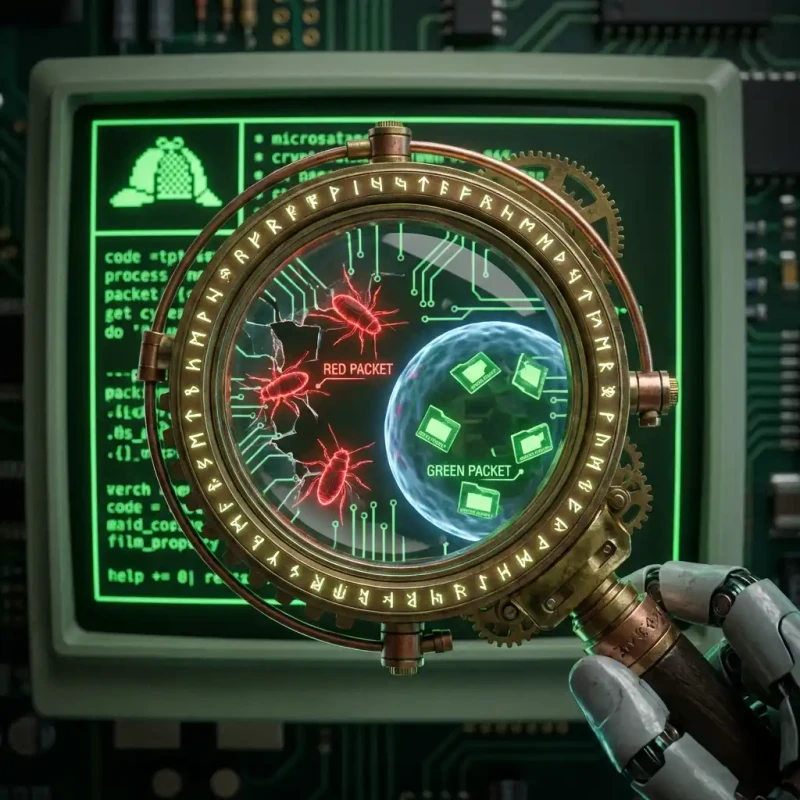
The Red Flag: As soon as you select a file, do you see a new row appear that says POST or PUT? Does the "Size" column start growing (e.g., 5MB, 10MB)?
The Verdict: That proves the file is being uploaded. No matter what their privacy policy says, your data is physically traveling to their server.
The "Payload" Inspection
If you are feeling brave, click on that POST request. Look for a tab called "Payload" or "Request Data." If you see weird code that includes your filename (e.g., "tax_return_2025.pdf"), you have caught them red-handed.
Step 3: The MojoDocs Audit
Now, try the same test on MojoDocs.
1. Open the Network tab.
2. Drag a file into our PDF merger.
3. Watch the radar.
The Result: Silence. You will see no new network requests for your file size. The "waterfall" graph stays flat. This is mathematical proof that the file stayed on your device.
Comparison: The Network Signature
| Signal | Cloud Tool (Unsafe) | MojoDocs (Safe) |
|---|---|---|
| Methods | POST / PUT requests | GET (for loading app only) |
| Data Payload | Matches File Size (e.g. 15MB) | ~0KB (Analytics pings only) |
| Destination | api.cloudconvert.com | N/A (Memory) |
Why Transparency Matters
We encourage this audit because the "Black Box" era of the web is over. Users deserve to know what is happening under the hood. If a tool company is afraid of you looking at their Network tab, run away.
Conclusion: Trust Your Eyes
You wouldn't eat food if you didn't know what was in it. Don't use software if you don't know where it talks to. Use the Network tab, audit your tools, and stick with the ones that pass the test.
Engineering Insight: XHR vs. Fetch
In the Network tab, look for XHR or Fetch type requests. These are the channels apps use to send data. MojoDocs only uses these to load the WebAssembly binary once at the start. After that, we cut the cord.